Updated April 2026. When evaluating ransomware protection strategies, most enterprise leaders quickly realize that perimeter defense alone is no longer sufficient. As hybrid work environments expand and digital transformations accelerate, malicious actors continuously refine their extortion tactics. Securing corporate infrastructure requires shifting from purely reactive firewall configurations toward a holistic, continuously evolving cybersecurity posture. You need a unified approach that weaves artificial intelligence, rigorous access controls, and robust recovery architectures directly into the fabric of your organization.
Threat syndicates no longer just encrypt files; they exfiltrate sensitive intellectual property, threaten public release, and demand exorbitant payouts under the guise of double or triple extortion. The integration of zero-trust frameworks, automated threat hunting, and immutable storage solutions forms the bedrock of enterprise defense against malware extortion. Building this resilience requires an active partnership between executive stakeholders, IT operations, and security teams to safeguard both critical operations and brand reputation.
What Are the Key Attack Vectors in Modern Ransomware?
Initial Compromise and Credential Theft
Understanding the entry points malicious actors exploit provides the baseline for any mature cybersecurity architecture. The initial compromise often occurs long before an actual encryption event takes place. Cybercriminals continuously scan for exposed vulnerabilities, leveraging sophisticated social engineering and automated exploitation scripts to breach defenses. A report from IBM Security in 2026 indicates that compromised credentials and phishing attacks account for 41% of all initial access vectors globally. Attackers actively seek out Remote Desktop Protocol (RDP) instances facing the public internet because RDP provides direct, authenticated access to network segments without requiring the exploitation of complex software vulnerabilities. Once an attacker obtains valid credentials, they can bypass traditional intrusion detection systems by masking their lateral movement as standard administrative activity.
The Evolution of Phishing Campaigns
Phishing campaigns have evolved beyond poorly worded emails. Modern syndicates utilize generative AI to craft highly personalized spear-phishing lures targeting specific executives based on their recent corporate filings or social media activity. In one recent case, a targeted employee in a financial services firm received a deepfake voice memo from their purported CEO authorizing an urgent software update, which ultimately deployed a custom trojan payload. This level of sophistication renders traditional security awareness training inadequate. Furthermore, software supply chain vulnerabilities introduce systemic risk. When attackers compromise a widely used third-party application, they inherit access to thousands of downstream clients simultaneously, circumventing local perimeter defenses entirely. See our detailed guide on Ransomware Threat Landscape Explained.
What failure looks like: A mid-sized logistics firm ignores anomalous off-hour logins originating from an unrecognized geopolitical region. By Monday morning, their entire global dispatch system is locked, halting operations and triggering immediate breaches in global privacy framework compliance, a scenario discussed in depth when analyzing international regulatory requirements. Without visibility into lateral movement, the organization remains unaware of the breach until the ransom note appears on administrative terminals.
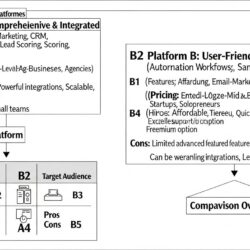
Foundational Tiers of Enterprise Defense

Securing an organization against sophisticated extortion schemes requires layered defensive mechanisms that operate independently yet share telemetry. Basic antivirus software cannot stop fileless malware that executes directly in computer memory. Instead, modern enterprise defense relies on a combination of endpoint detection, aggressive network segmentation, and identity-driven access controls.
Identity Verification and Network Architecture
Enforcing the principle of least privilege ensures that even if an attacker successfully compromises a standard user account, they cannot immediately escalate their permissions to access sensitive databases or critical infrastructure. This compartmentalization prevents a single compromised workstation from cascading into a catastrophic, organization-wide outage.
Lena Petrova: Implementing a true zero-trust architecture fundamentally shifts the defensive paradigm. We operate under the assumption that the network is already hostile. Every access request, whether internal or external, must be explicitly authenticated, authorized, and continuously validated before granting access to enterprise resources.
Organizations implementing robust zero trust models reduce breach costs by 34% compared to those without such frameworks, according to the Ponemon Institute’s 2025 Cost of a Data Breach Report. Consider a hospital network where administrative staff workstations operate on the same virtual LAN as critical life-support systems and patient record databases. If a billing specialist opens a malicious attachment, the flat network architecture allows the payload to rapidly spread to clinical machines. Aggressive network segmentation solves this by placing rigid firewalls between operational technology and standard IT environments. See our detailed guide on Essential Ransomware Prevention Techniques.
Core Security Layers Compared
| Defense Layer | Traditional Approach | Modern Framework |
|---|---|---|
| Identity Verification | Single-factor passwords | Phishing-resistant MFA (FIDO2) |
| Endpoint Security | Signature-based Antivirus | Behavioral EDR with Automated Containment |
| Network Architecture | Perimeter-focused (Castle-and-Moat) | Zero-Trust Network Access (ZTNA) |
| Data Backup | On-premises tape or attached NAS | Air-gapped, immutable cloud storage |
[INLINE IMAGE 2: Diagram comparing a legacy perimeter security model against a modern zero-trust architecture with segmented cloud environments.]
Artificial Intelligence Rewrites the Rules of Cybersecurity
Behavioral Heuristics and Anomaly Detection
The volume, velocity, and variety of network telemetry generated by modern enterprise environments exceed the analytical capacity of human security teams. Machine learning algorithms process millions of events per second, identifying subtle deviations from established operational baselines that indicate a stealthy intrusion. AI enhances defense by correlating seemingly disjointed events—such as an unusual PowerShell script execution followed by an anomalous data transfer to an unknown external IP address—into a unified incident alert. This behavioral heuristics model does not rely on known malware signatures, allowing the system to identify novel zero-day exploits based purely on the malicious actions they attempt to perform.
Automated Containment Protocols
Automated containment protocols isolate threats at machine speed. Research from CrowdStrike in 2026 demonstrates that AI-driven Endpoint Detection and Response (EDR) platforms can autonomously quarantine an infected host from the corporate network in an average of 14 seconds. This rapid response time effectively breaks the kill chain before the malware can establish command-and-control communications or begin encrypting localized files. When a financial institution recently deployed an automated Security Orchestration, Automation, and Response (SOAR) platform, they configured the AI to instantly revoke session tokens for any user exhibiting irregular access patterns. A subsequent credential stuffing attack succeeded in guessing a password, but the AI blocked the login attempt because the keyboard cadence and geographic location fell outside the user’s historical norms.
What success looks like: A spear-phishing payload successfully executes on a marketing endpoint, but the AI-driven behavioral models instantly detect the process attempting to modify system registries. The platform isolates the workstation and suspends the compromised user account before lateral movement begins, reducing the threat dwell time to mere seconds. Integrating these advanced algorithms requires careful consideration when selecting appropriate AI integration architectures to ensure seamless deployment across legacy systems. See our detailed guide on AI in Cybersecurity: Ransomware Detection & Response.
How Do Digital Transformation and Security Intersect?

Cloud Migration Risks
Accelerated cloud migration and the permanent shift toward distributed workforces have dissolved traditional enterprise perimeters. As businesses adopt multi-cloud environments, serverless computing, and edge devices, the attack surface expands exponentially. Misconfigured Identity and Access Management (IAM) roles frequently grant overly broad permissions, creating unintended pathways for data exfiltration. Cloud adoption expands the attack surface because administrators often apply legacy on-premises security paradigms to dynamic cloud infrastructure, resulting in publicly accessible storage buckets or exposed application programming interfaces (APIs). Cybersecurity must integrate natively into the continuous integration and continuous deployment (CI/CD) pipeline, shifting security protocols left in the development lifecycle.
Supply Chain Vulnerabilities
According to Gartner (2026), 68% of targeted attacks in highly digitized supply chains exploit trusted third-party vendor connections. A manufacturing firm recently accelerated their digital transformation by connecting IoT sensors on their factory floor directly to a cloud analytics platform. However, they neglected to implement mutual TLS authentication for the devices. Attackers intercepted the unencrypted traffic, injected malicious code into the data stream, and successfully deployed malware across the analytics cluster. This incident underscores the necessity of embedding security directly into the business strategy, rather than treating it as an operational afterthought.
Securing the modern enterprise also requires a cultural transformation. The technological solutions must be matched by human vigilance, which is why training employees for complex technical integrations is a non-negotiable aspect of operational resilience. Employees must understand how to interact securely with new cloud platforms and AI-assisted workflows. See our detailed guide on Cybersecurity for Digital Transformation.
[INLINE IMAGE 4: Infographic mapping cloud migration phases to their corresponding security checkpoints and risk mitigation protocols.]
Protocols for Incident Response and Data Recovery
The 3-2-1 Backup Strategy and Immutability
Even the most advanced preventative measures cannot guarantee absolute immunity from cyber threats. A mature cybersecurity posture heavily weights its resources toward rapid recovery and incident response (IR) capabilities. True operational resilience is determined not solely by the ability to block an attack, but by the organization’s capacity to restore critical services quickly following a successful breach. Implementing the 3-2-1 backup strategy—maintaining three copies of data, across two different media types, with one copy stored offsite—remains foundational, but it must be modernized with hardware-enforced immutability.
Immutability prevents malicious software from encrypting or deleting backups because the storage infrastructure enforces a write-once-read-many (WORM) policy at the lowest hardware or cloud-provider layer. According to the Veeam Data Protection Trends 2026 report, organizations utilizing immutable storage solutions report a 92% successful recovery rate without engaging in ransom negotiations. By physically and logically separating the backup infrastructure from the primary production domain, a process known as air-gapping, administrators ensure that compromised active directory credentials cannot be leveraged to destroy the safety net.
Executing the Incident Response Plan
Lena Petrova: An incident response plan that exists only on paper is functionally useless during a crisis. Organizations must conduct quarterly tabletop exercises involving legal, public relations, and executive leadership—not just the IT department—to build muscle memory for actual critical events.
During an active cyber extortion event, time is the critical variable. First responders must immediately disconnect affected subnetworks, preserve memory captures for forensic analysis, and initiate out-of-band communication channels. Relying on corporate email during a breach often tips off the attackers to the defense strategy. See our detailed guide on Ransomware Incident Response Planning.
Common Mistakes in Security Architecture
Organizations frequently undermine their own substantial cybersecurity investments by neglecting fundamental administrative hygiene or harboring dangerous misconceptions about how modern malware propagates. A failure to address legacy technical debt provides cybercriminals with simple, undocumented avenues directly into the core network. Examining past breaches reveals a consistent pattern of avoidable architectural errors that facilitated catastrophic data loss.
- Maintaining Flat Network Topologies: Flat networks facilitate rapid lateral movement. Once a perimeter is breached, an attacker faces zero internal firewalls, allowing them to pivot from an unsecured IoT device directly to the central financial database.
- Ignoring Service Accounts: IT departments often create highly privileged service accounts for automated application integrations but fail to rotate their passwords or monitor their usage. Attackers frequently hijack these dormant, hyper-privileged accounts to deploy widespread encryption scripts invisibly.
- Storing Backups on the Primary Domain: If the backup server is joined to the same Active Directory domain as the rest of the enterprise, a domain-wide compromise will instantly grant the attackers the permissions necessary to delete the backups before initiating the encryption of production data.
- Treating Security as an IT-Only Issue: Treating a cyber breach solely as a technical failure rather than a comprehensive business continuity crisis leads to chaotic external communications, regulatory fines, and severe reputational damage.
One notable incident involved a healthcare provider that invested heavily in next-generation firewalls but failed to disable default administrative credentials on their newly installed virtual private network (VPN) appliances. Within days of deployment, automated scanners identified the vulnerability, leading to a massive data exfiltration event. See our detailed guide on Avoiding Ransomware Mistakes.
The Trajectory of Threat Mitigation Technologies
Quantum Computing and Cryptography
The adversarial landscape is shifting rapidly as cybercriminals begin adopting the same advanced technologies used by enterprise defenders. Preparing for the next decade of threats requires looking beyond current defensive paradigms toward emerging cryptographic standards and distributed ledger technologies. Quantum computing poses a severe, looming threat to current RSA encryption standards because Shor’s algorithm can factor large prime numbers exponentially faster than classical computers, theoretically breaking the encryption securing the global financial system.
Blockchain for Data Integrity
To counter this, organizations are beginning to transition toward quantum-resistant algorithms mandated by institutions like the National Institute of Standards and Technology (NIST). Concurrently, the application of blockchain technology is moving beyond cryptocurrencies into data integrity verification. By anchoring cryptographic hashes of critical system configurations and backup states to a decentralized ledger, administrators can mathematically prove whether data has been tampered with by a malicious actor. This concept is closely related to the structural shifts occurring within decentralized internet architectures, where data provenance becomes cryptographically verifiable.
Ultimately, implementing effective defense protocols requires a dynamic, forward-looking mindset. Threat actors will leverage AI to automate vulnerability discovery and craft undetectable payloads, meaning enterprise defenses must operate autonomously to match that speed. Continuous adaptation, rigorous architectural reviews, and an unwavering commitment to operational resilience will dictate which organizations survive the increasingly hostile digital landscape. See our detailed guide on Emerging Ransomware Defense Technologies.
Sources & References
- IBM Security. (2026). Cost of a Data Breach Report 2026. Armonk, NY: IBM Corporation.
- Ponemon Institute. (2025). The State of Zero Trust Architecture. Traverse City, MI: Ponemon Institute.
- CrowdStrike. (2026). Global Threat Report: The AI Acceleration in Cyber Warfare. Austin, TX: CrowdStrike.
- Gartner, Inc. (2026). Strategic Predictions for Supply Chain Security. Stamford, CT: Gartner.
- Veeam Software. (2026). Data Protection Trends Report. Columbus, OH: Veeam.
About the Author
Lena Petrova, Principal AI Ethicist & Futures Strategist (Certified AI Ethics Practitioner, Former Lead, UNESCO Global AI Policy Forum) — I’m a passionate advocate for responsible innovation, guiding organizations to leverage AI ethically for sustainable growth and a human-centric future of work.
Reviewed by Kai Miller, Lead Content Strategist, AI & Innovation — Last reviewed: April 10, 2026