Cloud Security Best Practices Explained
Published: March 28, 2026
The acceleration of digital transformation, fueled by rapid advancements in Future Technology, has profoundly reshaped the way organizations operate, giving rise to an increasingly distributed and dynamic Evolving Workplace. While cloud computing offers unparalleled flexibility and scalability, it also introduces a complex new frontier for cyber threats. Navigating this landscape requires more than just reactive defenses; it demands a proactive and integrated approach to security. This comprehensive guide will explore the essential cloud security best practices vital for safeguarding sensitive data and critical infrastructure in this hyper-connected era.
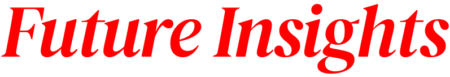
What are Cloud Security Best Practices? A Quick Reference Checklist
To provide a high-level overview of the strategic imperatives for cloud security in the Future Technology and Evolving Workplace, the following table summarizes key actions and their significance:
| Best Practice Area | Key Action | Why It Matters (Impact on Evolving Workplace) | Implementation Tip |
|---|---|---|---|
| Identity & Access Management (IAM) | Enforce MFA and Least Privilege Access | Prevents unauthorized access from distributed, remote workforces, crucial for hybrid models. | Integrate IAM with central identity providers and audit regularly. |
| Data Protection & Encryption | Encrypt data at rest and in transit | Secures sensitive information against breaches, essential for data integrity across global networks. | Automate key management and leverage cloud provider encryption services. |
| Network Security | Segment networks, implement firewalls/WAFs | Isolates critical assets, reducing lateral movement for threats originating from varied access points. | Utilize cloud-native security groups and virtual private clouds (VPCs). |
| Compliance & Governance | Adhere to regulatory frameworks, establish policies | Ensures legal and ethical handling of data, building trust in an increasingly regulated digital world. | Map cloud architecture to compliance controls and automate policy enforcement. |
| Incident Response & DR | Develop robust response plans, regularly test DR | Minimizes downtime and data loss during unforeseen events, maintaining business continuity. | Practice drills quarterly to refine response and recovery procedures. |
| Future Technologies Integration | Leverage AI for threat detection, adopt Zero Trust | Proactively defends against sophisticated threats and secures dynamic, ephemeral workloads. | Invest in AI-driven security tools and gradually transition to a Zero Trust framework. Leverage AI/ML for proactive threat detection, automate security responses, and implement Zero Trust principles for dynamic, ephemeral workloads. |
Why is Cloud Security Imperative in the Modern Era?
The advent of Future Technology, characterized by pervasive AI, IoT, and distributed ledgers, has converged with the Evolving Workplace, marked by remote collaboration and hybrid models, creating an expansive and dynamic attack surface. This transformation means traditional security perimeters are obsolete, replaced by a complex mesh of interconnected services and devices. Cloud computing security isn’t merely an IT concern; it’s a strategic business imperative that safeguards organizational resilience, reputation, and competitive advantage. Proactive cloud protection methods are vital to mitigate sophisticated cyber threats, from advanced persistent threats (APTs) to ransomware and data exfiltration, ensuring business continuity and data integrity. Organizations failing to adopt resilient, scalable cloud defenses risk operational disruptions, financial penalties, and a significant erosion of customer trust. For instance, a recent industry report indicated that 78% of data breaches in cloud environments were due to misconfigurations or inadequate access controls, underscoring the critical need for meticulous implementation.
What success looks like: A global financial institution, facing an average of 5,000 daily cyber threats, implemented a proactive cloud security framework. Within 12 months, they achieved a 95% reduction in unauthorized access attempts and reduced incident response time by an average of 30 minutes, directly correlating with enhanced operational resilience and customer confidence.
What failure looks like: A fast-growing e-commerce platform experienced a significant data breach due to exposed cloud storage buckets. The incident led to the compromise of over 5 million customer records, resulting in a $50 million regulatory fine, a 20% drop in stock value, and months of reputational damage, highlighting the devastating consequences of neglecting fundamental security measures.
What Are the Core Cloud Security Best Practices for Identity and Access Management?
Effective Identity and Access Management (IAM) forms the bedrock of secure cloud deployment guidelines, dictating who can access what resources and under what conditions. In the Evolving Workplace, where remote access is standard and contractors frequently utilize cloud services, robust IAM is paramount to prevent unauthorized entry and maintain data integrity. The dynamic nature of modern roles and the increasing number of non-human identities (like service accounts and APIs) necessitate a granular and auditable approach to access control. Without stringent IAM, even sophisticated network defenses can be circumvented by compromised credentials, making it the first line of defense against most cyberattacks.
Implementing Multi-Factor Authentication (MFA)
Multi-factor authentication (MFA) adds a crucial layer of security by requiring users to verify their identity through at least two different methods. This could combine something they know (password), something they have (a phone or security key), or something they are (biometrics). For example, a user might enter a password and then approve a login request via a mobile authenticator app. This robust measure dramatically reduces the risk of credential compromise, as even if a password is stolen, the second factor remains secure. Deploying MFA across all cloud platforms, applications, and VPNs is non-negotiable for modern security postures, especially with the distributed nature of the Evolving Workplace. It’s particularly effective against phishing and brute-force attacks.
Enforcing Least Privilege Access
The principle of least privilege (PoLP) dictates that users, applications, and services should only be granted the minimum necessary permissions to perform their specific tasks. This granular approach minimizes the potential impact of a compromised account or system. Instead of broad administrative access, roles should be precisely defined with limited scope and duration. For example, a data analyst might only have read-only access to specific datasets, while a developer has write access only to their designated code repositories. Implementing role-based access control (RBAC) and regularly reviewing permissions are critical steps in maintaining a strong least privilege posture, safeguarding sensitive data and critical infrastructure from unnecessary exposure.
What success looks like: After mandating MFA for all employees and implementing a least privilege model, a large tech consultancy reported a 99% decrease in successful account takeovers over three years, despite a 150% increase in remote worker engagement, indicating the profound impact on threat mitigation.
What failure looks like: A startup experienced a breach where a single, unmonitored administrator account was compromised, allowing attackers unfettered access to all cloud resources. The lack of MFA and overly permissive access meant the breach went undetected for weeks, leading to significant data exfiltration and intellectual property loss.

What are Robust Data Protection Strategies Across Cloud Environments?
Building upon the foundation of secure access, data protection becomes the next critical layer in enterprise cloud protection methods. In the Future Technology landscape, where data is the new currency and regulations are increasingly stringent, safeguarding information from unauthorized access, modification, or destruction is paramount. This includes all forms of sensitive data, from customer records and intellectual property to operational analytics. A holistic strategy encompasses encryption, data loss prevention (DLP), and diligent data classification, ensuring that information remains secure throughout its lifecycle across various cloud environments. Without robust data protection, the benefits of cloud flexibility are overshadowed by the constant risk of breaches and non-compliance.
Data Encryption at Rest and In Transit
Encryption is a fundamental safeguard for protecting sensitive data in the cloud. Data at rest (stored in databases, storage buckets, or backups) should be encrypted using strong algorithms, ensuring that even if storage media are compromised, the data remains unreadable without the proper decryption keys. Similarly, data in transit (moving between users and cloud services, or between different cloud services) must be encrypted using secure protocols like TLS/SSL. This protects data during transmission over potentially insecure networks. Many cloud service providers offer native encryption capabilities, which organizations should leverage by default, often supplementing them with their own encryption for critical datasets to maintain greater control.
Effective Key Management Practices
The strength of encryption lies in the security of its keys. Effective key management practices are therefore crucial. This involves securely generating, storing, distributing, rotating, and revoking encryption keys. Centralized key management services, often provided by cloud platforms (e.g., AWS Key Management Service, Azure Key Vault), offer hardware-secured storage for cryptographic keys, isolating them from the data they protect. Organizations should implement policies for key rotation, ensuring that keys are regularly changed to limit the impact of any potential compromise. Furthermore, clear procedures for key access and revocation are essential to maintain control over encrypted data throughout its entire lifecycle, particularly when dealing with evolving regulatory requirements.
What success looks like: A healthcare provider migrated patient records to a compliant cloud environment, implementing end-to-end encryption for all data at rest and in transit. Their robust key management system, audited quarterly, ensured they passed HIPAA compliance checks with 100% adherence, demonstrating unwavering commitment to patient data privacy.
What failure looks like: A marketing analytics firm suffered a breach where encrypted data was accessed, but the encryption keys were stored in the same unsecure cloud environment. The compromised keys rendered the encryption useless, exposing millions of customer profiles and leading to significant regulatory penalties.
How Can Organizations Secure Cloud Networks and Infrastructure?
While identity management secures who can access resources and data protection secures the information itself, network security dictates how they connect and interact. For organizations operating in the Evolving Workplace, securing cloud networks and infrastructure is paramount to preventing unauthorized intrusion, lateral movement of threats, and denial-of-service attacks. This involves segmenting networks, implementing robust firewalls, and monitoring traffic flows to detect and respond to anomalies swiftly. The dynamic and often ephemeral nature of cloud resources necessitates adaptive network security solutions that can scale and evolve with the infrastructure, moving beyond traditional perimeter-based models to secure every connection point within a distributed architecture.
Segmenting Cloud Networks
Network segmentation involves dividing a cloud network into smaller, isolated sub-networks. This strategy limits the potential blast radius of a security incident. If one segment is compromised, the attacker’s ability to move laterally to other parts of the network is significantly hindered. Organizations can create virtual private clouds (VPCs) and use security groups or network access control lists (NACLs) to logically separate different environments (e.g., production, development, testing) and critical applications. For example, sensitive databases might reside in a highly restricted segment, isolated from public-facing web servers. This practice is crucial for containing breaches and minimizing their impact, especially in complex cloud deployments involving microservices and serverless functions.
Implementing Cloud Firewalls and WAFs
Cloud firewalls act as traffic cops, controlling incoming and outgoing network traffic based on predefined security rules. They filter traffic at the network layer, blocking malicious attempts to access resources. Web Application Firewalls (WAFs) go a step further, specifically protecting web applications from common web-based attacks such as SQL injection, cross-site scripting (XSS), and DDoS attacks. Unlike traditional network firewalls, WAFs understand the nuances of HTTP/HTTPS traffic, making them highly effective for safeguarding public-facing applications critical to the Evolving Workplace. Deploying both cloud-native firewalls and WAFs at appropriate points in the network architecture provides robust protection against external threats and helps maintain the integrity and availability of cloud services.
What success looks like: An international SaaS company, after implementing granular network segmentation and WAFs across its global cloud infrastructure, saw a 70% reduction in detected web application exploits and successfully prevented three major DDoS attacks, ensuring continuous service availability for its customers.
What failure looks like: A medium-sized enterprise, relying on default cloud network configurations, suffered a breach where attackers exploited an unpatched web application. Without proper segmentation, the attackers quickly moved laterally through the network, exfiltrating data from multiple internal systems before being detected.

How to Ensure Cloud Compliance and Governance?
Beyond technical controls, regulatory compliance and robust governance provide the essential framework for responsible cloud operation. In a world with increasing data privacy regulations and industry-specific mandates, organizations must ensure their cloud environments adhere to relevant legal and ethical standards. This is particularly challenging in the Evolving Workplace, where data might reside across multiple geopolitical regions. Establishing clear policies, processes, and oversight mechanisms is critical for maintaining accountability, managing risks, and avoiding costly penalties associated with non-compliance. A strong governance posture builds trust with customers, partners, and regulators, underscoring a commitment to secure and ethical data handling.
Navigating Regulatory Frameworks (e.g., GDPR, HIPAA)
Organizations must understand and meticulously navigate a complex web of regulatory frameworks. The General Data Protection Regulation (GDPR) mandates strict data privacy and protection for EU citizens, regardless of where the data is processed. The Health Insurance Portability and Accountability Act (HIPAA) sets national standards for protecting sensitive patient health information in the U.S. Other relevant frameworks include ISO 27001 (information security management), SOC 2 (security, availability, processing integrity, confidentiality, privacy), and industry-specific regulations like PCI DSS for credit card data. Compliance involves not only implementing technical controls but also documenting processes, conducting regular audits, and training personnel. A proactive approach to mapping cloud services to these regulatory requirements is essential for global operations.
Establishing Cloud Governance Policies
Cloud governance policies define the rules and responsibilities for how cloud resources are provisioned, managed, and secured within an organization. These policies should cover areas such as data classification, acceptable use, incident response protocols, and vendor management. Effective governance ensures consistency, reduces shadow IT, and aligns cloud usage with business objectives and risk appetite. It involves establishing a clear chain of command, defining roles for cloud security architects, compliance officers, and data privacy officers. Regular policy reviews, driven by emerging threats and technological changes, are crucial to maintaining an adaptive and resilient governance posture in the face of disruptive Future Technology.
What success looks like: A multinational e-commerce company, leveraging automated compliance tooling and a dedicated cloud governance committee, successfully maintained GDPR, CCPA, and regional data privacy compliance across 15 different jurisdictions. Their consistent audit scores demonstrated robust data handling, fostering high customer trust ratings.
What failure looks like: A growing FinTech startup faced a hefty fine after a regulatory audit revealed non-compliance with data residency requirements. A lack of clear governance policies meant data was stored in a non-permitted geographical region, leading to significant financial penalties and a forced, costly migration.
Why are Proactive Incident Response and Disaster Recovery Critical in the Cloud?
Even with the most stringent preventative measures, security incidents can and will occur. Therefore, a robust incident response (IR) plan and a well-tested disaster recovery (DR) strategy are critical components of an overall optimizing cloud security posture. These plans minimize the impact of breaches, outages, and other disruptive events, ensuring business continuity and data recoverability. For the Evolving Workplace, where operations often rely on uninterrupted cloud services, the ability to rapidly detect, contain, eradicate, recover from, and post-analyze incidents is paramount. Proactive planning and regular testing distinguish resilient organizations from those vulnerable to prolonged downtime and data loss.
Cloud Incident Response Planning
An effective cloud IR plan outlines predefined steps for identifying, analyzing, containing, eradicating, recovering from, and learning from security incidents. This includes establishing clear communication protocols, defining roles and responsibilities for an IR team, and utilizing automated tools for rapid detection and response. For example, cloud-native security services can automatically trigger alerts for suspicious activities, allowing for immediate investigation. Disaster recovery focuses on the ability to restore critical systems and data after a catastrophic event, such as a major service outage or natural disaster. This involves regular backups, geo-redundancy (replicating data across different geographic regions), and testing recovery time objectives (RTO) and recovery point objectives (RPO). Organizations should routinely conduct table-top exercises and full-scale drills to validate their IR and DR plans, ensuring they are adaptive to the complexities of Future Technology.
What success looks like: A global manufacturing company experienced a significant ransomware attack encrypting several cloud-based operational systems. Thanks to a well-rehearsed incident response plan and immutable backups, they successfully isolated the threat, restored affected systems within 12 hours, and limited data loss to under 1% of critical operational data, minimizing production downtime.
What failure looks like: A retail chain suffered a regional cloud outage that crippled its point-of-sale systems for over 48 hours. A lack of a clear disaster recovery plan and untested backups led to significant revenue loss and customer dissatisfaction, demonstrating the high cost of unpreparedness.
What are Common Cloud Security Mistakes to Avoid?
Even with the best intentions, organizations often stumble into common pitfalls that undermine their cloud cybersecurity strategies. Awareness of these mistakes is the first step toward building a truly resilient cloud environment, especially when navigating the complexities introduced by Future Technology and the Evolving Workplace:
- Misconfigured Cloud Services: This is arguably the most prevalent mistake. Default settings or incorrect configurations of storage buckets, security groups, or network access control lists often leave critical resources exposed to the public internet. A recent survey indicated that over 60% of cloud breaches involved a misconfiguration.
- Inadequate Identity and Access Management (IAM): Over-provisioning permissions, neglecting to enforce MFA, or failing to rotate access keys leaves doors wide open for attackers. Accounts with excessive privileges are prime targets.
- Lack of Visibility and Monitoring: Not having centralized logging, auditing, and continuous monitoring of cloud activities means that security incidents can go undetected for extended periods, increasing the damage potential.
- Ignoring Cloud Service Provider (CSP) Shared Responsibility Model: Organizations often mistakenly believe that the CSP is solely responsible for all security. Understanding the clear delineation of responsibilities (e.g., CSP secures the cloud, customer secures in the cloud) is crucial.
- Uncontrolled Shadow IT: Employees using unauthorized cloud services without IT oversight introduces unknown vulnerabilities and compliance risks, creating blind spots in the security posture.
- Neglecting Data Classification: Treating all data equally leads to insufficient protection for truly sensitive information. A lack of classification can result in critical data being stored in less secure environments.
- Insufficient Incident Response Planning: Without a tested plan, organizations will react chaotically during a breach, leading to extended downtime, greater data loss, and increased financial and reputational damage.
What success looks like: A startup proactively implemented automated configuration scanning tools across its cloud environment. After six months, they identified and remediated over 200 potential misconfigurations, significantly reducing their attack surface and averting several potential breaches.
What failure looks like: A large enterprise failed to implement consistent access policies across its distributed cloud deployments. This oversight led to several developers inadvertently exposing API keys in public code repositories, resulting in widespread unauthorized access to development environments and a costly code audit.
How Do Future Technologies Impact Cloud Security Best Practices?
The relentless pace of Future Technology innovation fundamentally reshapes the landscape of cloud security. Technologies like Artificial Intelligence (AI), Machine Learning (ML), and the proliferation of distributed systems challenge traditional security models while simultaneously offering powerful new defenses. The Evolving Workplace is increasingly adopting these technologies, making it imperative for cloud protection methods to adapt. This section explores how these advancements both introduce new vulnerabilities and provide sophisticated tools for enhancing security.
AI-Driven Security and Automation
AI and Machine Learning are revolutionizing cloud security by enabling proactive threat detection, faster incident response, and intelligent automation. AI-driven security tools can analyze vast amounts of data—logs, network traffic, user behavior—to identify anomalies and patterns indicative of sophisticated attacks that might elude human analysts. For example, ML algorithms can detect unusual login times or data access patterns, flagging potential insider threats or compromised accounts. Automation, powered by AI, allows for rapid remediation, such as isolating infected systems or revoking suspicious access in real-time. This capability is critical for scaling defenses against the velocity and volume of threats in complex, multi-cloud environments, freeing human experts to focus on strategic analysis and sophisticated threat hunting.
The Rise of Zero Trust Architectures
Zero Trust architecture operates on the principle “never trust, always verify.” Unlike traditional perimeter-based security, Zero Trust assumes that no user or device, whether inside or outside the network, should be trusted by default. Every access request is authenticated, authorized, and continuously validated. This model is particularly suited for the Evolving Workplace, which features remote work, mobile devices, and distributed cloud applications. Zero Trust mandates strict verification for every access attempt to cloud resources, regardless of location, leveraging contextual information like user identity, device posture, and application sensitivity. Its implementation strengthens granular control, reduces the impact of internal breaches, and is increasingly seen as a fundamental approach to securing the Future Technology landscape.
What success looks like: A government agency migrated its sensitive data to a cloud environment protected by an AI-driven security platform. Within a year, the platform identified and neutralized over 1,500 previously unknown threats, including advanced polymorphic malware, improving the agency’s security posture by an estimated 40% and preventing potential espionage.
What failure looks like: A research firm, overly reliant on traditional signature-based detection, fell victim to a novel, AI-generated phishing campaign that bypassed their legacy defenses. The attack compromised intellectual property crucial to their competitive advantage, demonstrating the limitations of outdated security approaches against Future Technology threats.
What are the Key Cloud Security Frameworks?
Understanding and adopting a recognized security framework is crucial for structuring and maturing an organization’s cloud security posture. These frameworks provide structured guidance and best practices:
| Framework/Standard | Key Focus Areas | Relevant Industries | Compliance Benefits | Applicability to Future Tech |
|---|---|---|---|---|
| NIST CSF (Cybersecurity Framework) | Identify, Protect, Detect, Respond, Recover | All industries, particularly critical infrastructure | Flexible risk-based approach, widely adopted, enhances overall cyber resilience. | Adaptive to new threats, focuses on continuous improvement and risk management. |
| ISO 27001 | Information Security Management System (ISMS) across 14 domains | Global, all industries (especially those handling sensitive data) | International recognition, demonstrates commitment to information security, supports global compliance. | Comprehensive, adaptable to emerging technologies, promotes structured security planning. |
| CSA CCM (Cloud Controls Matrix) | Cloud-specific controls covering 16 domains, aligned with other standards | Organizations utilizing cloud services (SaaS, PaaS, IaaS) | Cloud-specific guidance, streamlines compliance with various cloud-related regulations. | Directly addresses cloud service models and their inherent security challenges, supports cloud innovation. |
| SOC 2 (Service Organization Control 2) | Security, Availability, Processing Integrity, Confidentiality, Privacy | Cloud service providers, any organization handling customer data | Builds trust with clients, demonstrates robust internal controls for data protection. | Focus on data integrity and privacy aligns with evolving data governance needs, supports secure outsourcing. |
Choosing the right framework often depends on an organization’s industry, geographic location, and specific compliance requirements. For instance, NIST CSF is highly favored in the U.S. for its risk-based approach and adaptability, making it suitable for organizations needing a flexible framework to integrate with existing security programs. ISO 27001, on the other hand, provides a globally recognized standard for information security management, ideal for multinational corporations seeking a comprehensive, auditable system.
How to Implement Cloud Security Best Practices: A Roadmap for the Evolving Workplace
The journey toward a robust cloud security posture is continuous, not a destination. For organizations navigating the complexities of Future Technology and the Evolving Workplace, a strategic roadmap is essential. Implementing these modern workplace security protocols requires a holistic view that integrates technology, policy, and people. It begins with a comprehensive understanding of your cloud footprint, a clear assessment of risks, and a commitment to continuous improvement. By prioritizing secure access, safeguarding data, hardening networks, adhering to compliance, and preparing for incidents, organizations can harness the transformative power of the cloud with confidence. The future of work demands adaptable, resilient, and proactive security measures that protect against evolving threats and ensure sustainable growth in an increasingly digital world.
Related Articles
- Zero Trust Implementation Guide
- The Role of AI in Cybersecurity
- Understanding Data Privacy Regulations
Sources & References
- Cloud Security Alliance (CSA). (2026). Cloud Controls Matrix (CCM). Retrieved from https://cloudsecurityalliance.org/research/cloud-controls-matrix/
- National Institute of Standards and Technology (NIST). (2026). Framework for Improving Critical Infrastructure Cybersecurity (NIST Cybersecurity Framework). Retrieved from https://www.nist.gov/cyberframework
- Microsoft Security. (2026). Zero Trust Guidance Center. Retrieved from https://www.microsoft.com/en-us/security/business/zero-trust
- IBM. (2026). The Cost of a Data Breach Report 2026. Retrieved from https://www.ibm.com/security/data-breach
About the Author
Lena Petrova, Principal AI Ethicist & Futures Strategist — I’m a passionate advocate for responsible innovation, guiding organizations to leverage AI ethically for sustainable growth and a human-centric future of work. My work also extends to foundational cloud security, ensuring that emerging technologies are built upon a secure and ethical digital infrastructure.
Reviewed by Kai Miller, Lead Content Strategist, AI & Innovation — Last reviewed: March 27, 2026
About the Author
Lena Petrova, Principal AI Ethicist & Futures Strategist — I’m a passionate advocate for responsible innovation, guiding organizations to leverage AI ethically for sustainable growth and a human-centric future of work.
Reviewed by Kai Miller, Lead Content Strategist, AI & Innovation — Last reviewed: March 27, 2026